When working with private keys that are protected with a passphrase on Ubuntu server you will be prompted you to enter the passphrase on each use. Just like on your desktop environment you can however use an SSH agent in which you load your keys for the duration of your session.
Continue reading “Using SSH agent on Ubuntu server”Changing your default kernel
A while back my laptop running Ubuntu started hanging on boot after a kernel update, to make it work I had to revert to using an earlier kernel version from the boot screen.
Its a bit inconvenient to have to do this manually every time you boot your machine, you can however change the default boot option that is used by grub. You can do this by editing /etc/default/grub and setting GRUB_DEFAULT to the item to select and then running sudo update-grub.
Using OpenSSL to verify downloads
Hashes are commonly offered by download pages for you to verify the integrity of your downloaded files. I typically verify these hashes using OpenSSL which supports many types of hashing algorithms and is available on many unix-like systems (and can often be installed on them easily enough if it is not yet present).
The basic method for verification works as follows: after downloading a file enter the command openssl {hashalgorithm} {/path/to/downloaded.file} to calculate a hash based on the file’s contents. If the hash shown matches the hash on the download page the file is as intended.
Scripting tmux
I spend quite a bit of time on the shell, more often than not inside a tmux session. For those of you not familiar with tmux, it is a terminal multiplexer (akin to GNU screen) allowing you to split your terminal into multiple windows and panes. Its a tool that offers man conveniences such as being able to start a session on a server, detach from it and to come back to later (in a different SSH session) or even having multiple people sharing a single session without having to physically be in the same place.
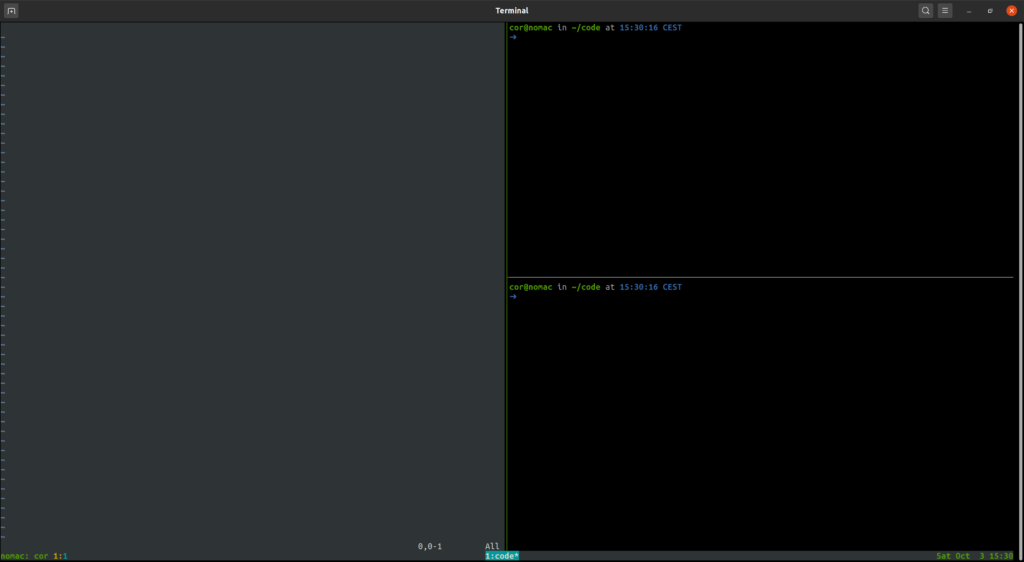
When developing with Ruby I tend to program using Vim in a tmux session. In my setup I usually have a window per project which has three panes: one for Vim, a second to run processes in (such as a rails web server) and a third as a console to run ad-hoc commands or an application console. With my configuration this setup looks something like the below screenshot:
While you can easily create the above panes with a few keystrokes, you can also script tmux to setup this up for you with a single key combination. This is what I will be diving into in this article.
Continue reading “Scripting tmux”Flushing your DNS cache on Ubuntu 20.04
Often enough I run into this little problem: I make a DNS change and want to see the results. When I check for the changes though it looks as if nothing has changed, and sometimes this is caused by my system’s DNS cache.
Clearing the cache on Ubuntu 20.04 can be done with the following command: sudo systemd-resolve --flush-caches, you can verify that the caches have been emptied by following that up with the command systemd-resolve --statistics which then gives an output like shown below:
DNSSEC supported by current servers: yes
Transactions
Current Transactions: 0
Total Transactions: 21870
Cache
Current Cache Size: 0
Cache Hits: 6722
Cache Misses: 15158
DNSSEC Verdicts
Secure: 7783
Insecure: 21703
Bogus: 0
Indeterminate: 0 The text and numbers will vary per setup, the “Current Cache Size” should however display a value of 0 to indicate your cache has been cleard.
If you are running dnsmasq next to the standard systemd-resolve like I do, restarting dnsmasq (with sudo systemctl restart dnsmasq) will ensure its caches are cleared to (otherwise you may still end up getting cached results).
And that’s all that I have for this very short post. If you have feedback on this article or have questions based on its contents then feel free to reach out to me on Twitter or through e-mail.
Obtaining your external IP address from the command-line
Sometimes you need to know what your external IP address is, for example when you need to make use of a protected service where they need to (temporarily) add your IP address to their firewall’s allow list to allow you to connect to said service.
If you have a broadband connection at home it is possible that you have a fixed external IP address and that you already know what it is. If you are however visiting elsewhere you likely do not know what it is, a quick solution in such cases is to open your browser and use a site such as https://www.whatismyip.com/ to see what your external IP address is. But what if you need to know this on a Unix-like server that only offers a command-line interface (or if you simply prefer to use your shell)?
Continue reading “Obtaining your external IP address from the command-line”Using dnsmasq to run a local TLD
If you work on a lot of different projects you likely have a lot of different entries in your hosts file to point fake domains to localhost or one or more Vagrant boxes. This can be a bit of a pain to manage. If you’re running Linux, BSD or Mac OS then this article offers an option that might ease this problem a bit: dnsmasq.
In this article I will describe how to setup dnsmasq to run your own local (fake) top level domain for which all domains will route to localhost (or another IP address of choice, to point to a Vagrant box for example). While writing this article I used Ubuntu 20.04, if you are running another operating system that can run dnsmasq you may have to do things slightly differently… in that case: be ready to consult some manuals.
Continue reading “Using dnsmasq to run a local TLD”Using sed (the non-interactive command line text editor)
If you go to the sed webpage it tells you that it is a non-interactive command line text editor. Unlike interactive editors you do not spend time in sed, instead you invoke sed with a set of command line parameters and it directly outputs or writes its result.
I have often used it in Vagrant provisioning scripts to tweak configuration files, you can however also use it to extract information from text files (such as log files) and convert that into a different format (such as CSV). In this article I will demonstrate how you can use sed to do some of these things to give you some insight into it’s utility.
Continue reading “Using sed (the non-interactive command line text editor)”Tmux and SSH agent forwarding
When you normally connect to a machine using SSH and start a tmux session SSH agent forwarding (if you have that setup) will work normally. When you however detach your session and re-attach it later you will find that it no longer does, this is because the environment variables in the shell inside the tmux session refers to the same SSH_AUTH_SOCK that it did when you originally connected.
Recent enough versions of tmux have something that can fix this for you, if you execute the command tmux show-environment -s you will see a bunch of shell commands to set a series of environment variables. If you execute those it will update the SSH information in the shell and agent forwarding will work once again, a shortcut to doing this in a single line would be eval "$(tmux show-environment -s)".
If you have your own dotfiles on the destination machine you can make this happen automatically. For bash users there’s the PROMP_COMMAND environment variable (see https://www.johntobin.ie/blog/updating_environment_variables_from_tmux/), for zsh users (like myself) you can do this by specifying a precmd hook.
If you add the following to your .zshrc (or a file you source inside it) you can set this up:
function update_environment_from_tmux() {
if [ -n "${TMUX}" ]; then
eval "$(tmux show-environment -s)"
fi
}
add-zsh-hook precmd update_environment_from_tmuxThe above will ensure that the update_environment_from_tmux function is executed before each command that you execute, if you re-attach to a tmux session that is using zsh with the above loaded and execute an SSH related command (git pull, scp, sftp, ssh, etc.) it will first automatically update the SSH environment variables and then execute the command making it work seamlessly.
The update_environment_from_tmux function only evals the tmux show-environment -s command if you are inside a tmux session (which will set the TMUX environment variable).
